In my recent search for malicious websites, I found Hypschonerms.com. Learn how to remove Hypschonerms.com.
Blogs
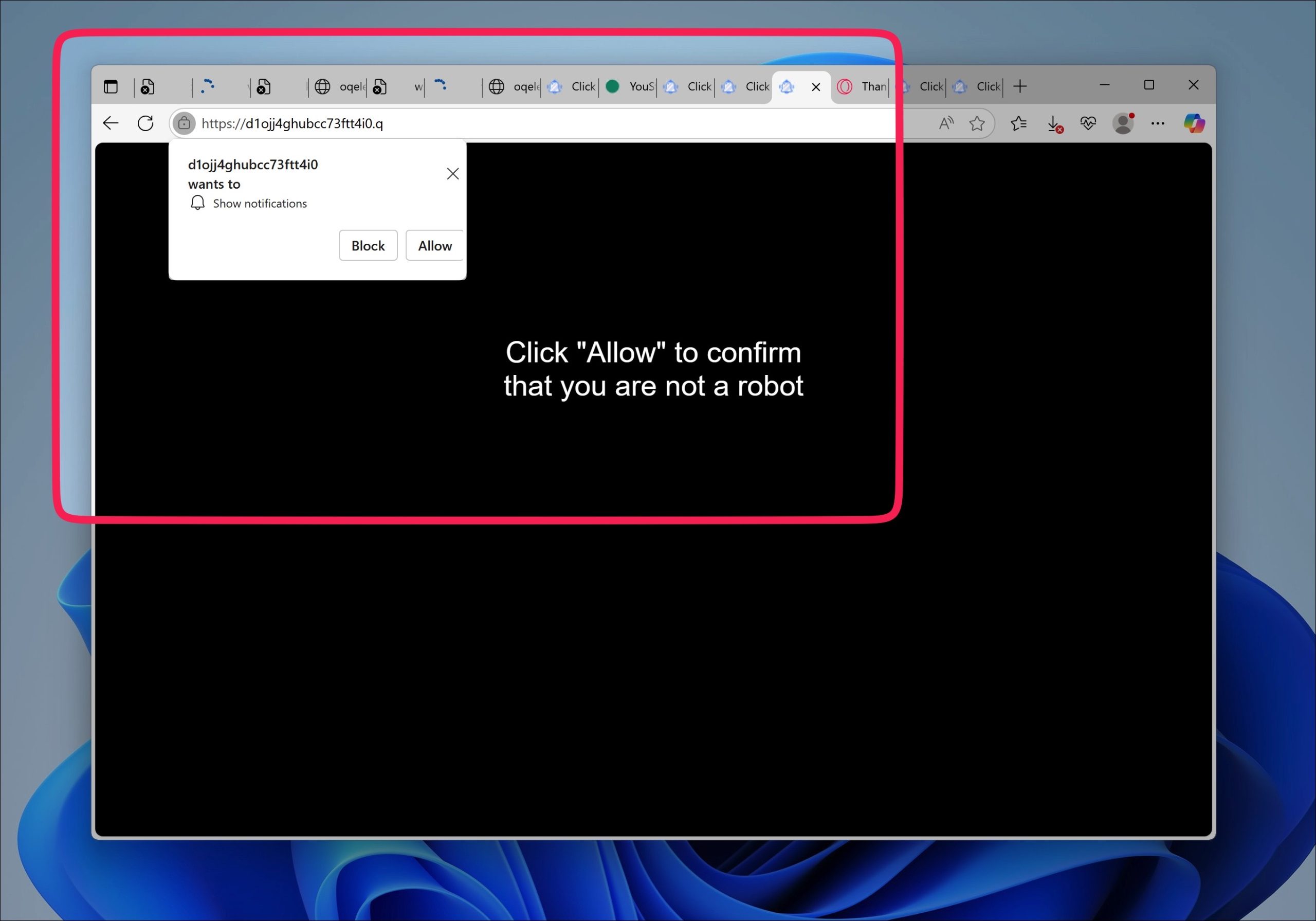
Bridgechainstudio.com removal instructions
In my recent search for malicious websites, I found Bridgechainstudio.com. Learn how to remove Bridgechainstudio.com.
Meatitenes.co.in removal instructions
In my recent search for malicious websites, I found Meatitenes.co.in. Learn how to remove Meatitenes.co.in.
Asw-confm.co.in removal instructions
In my recent search for malicious websites, I found Asw-confm.co.in. Learn how to remove Asw-confm.co.in.
Hjw-adguard.co.in removal instructions
In my recent search for malicious websites, I found Hjw-adguard.co.in. Learn how to remove Hjw-adguard.co.in.